Enabling Google Workspace SSO connections with your OVHcloud account
Objective
You can use Single Sign-On (SSO) to sign in to your OVHcloud account. To enable these connections, your account and Google Workspace accounts have to be using SAML (Security Assertion Markup Language) authentication.
This guide explains how to associate your OVHcloud account with an external Google Workspace service.
Requirements
- Being an administrator of a Google Workspace service
- An OVHcloud account
OVHcloud Control Panel Access
- Direct link: SAML SSO
- Navigation path:
Identity, Security & Operations>Users>SSO connection
Instructions
In order for a service provider (i.e. your OVHcloud account) to establish an SSO connection with an identity provider (i.e. your Google Workspace service), the key is to establish a mutual trust relationship by registering the SSO connection in both services.
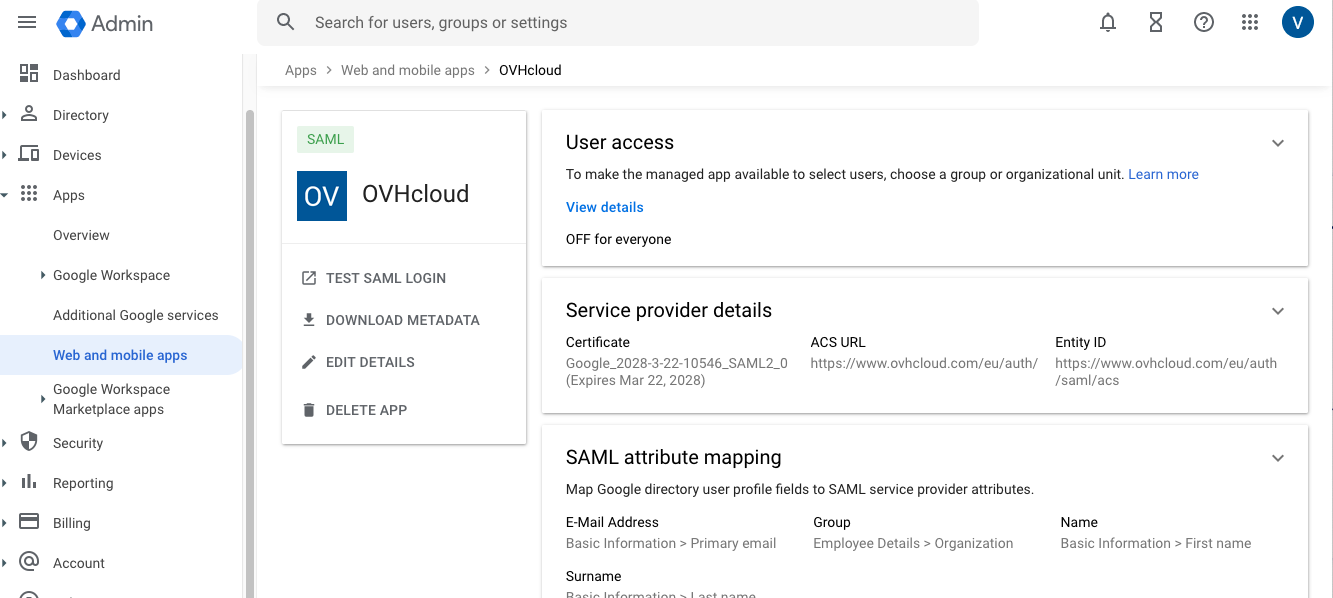
Registering OVHcloud into Google Workspace
Your Google Workspace acts as an identity provider. Requests to authenticate your OVHcloud account will only be accepted if you have first declared it as a trusted third party.
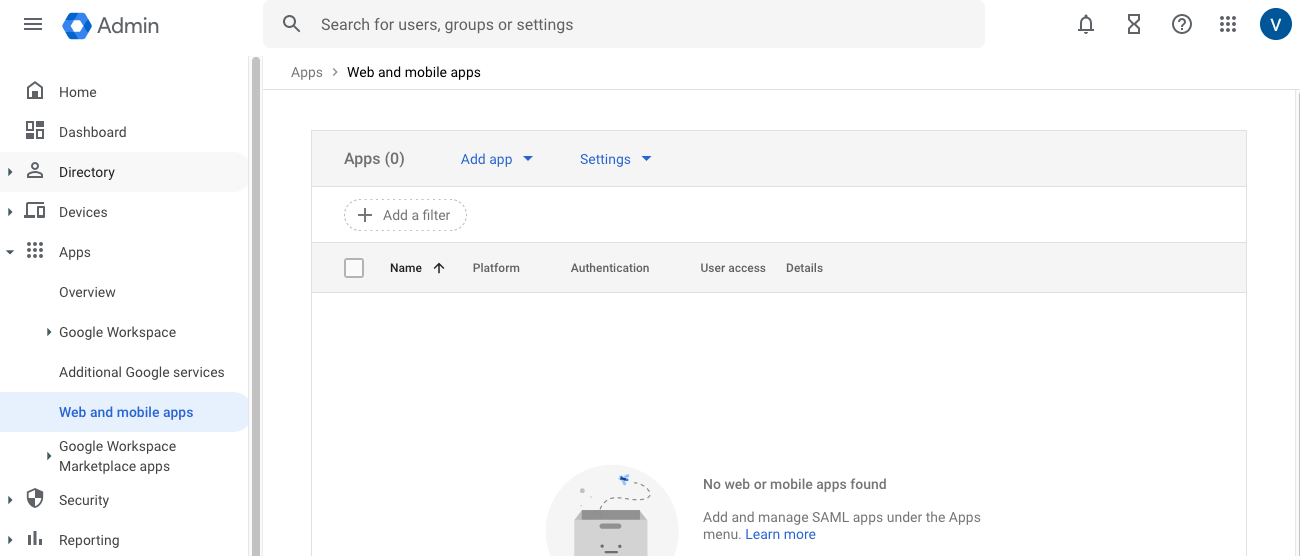
This means that it must be added as Web and mobile apps.
Log in to the Google Workspace administration interface with your administrator account.
Go to Apps then Web and mobile apps.
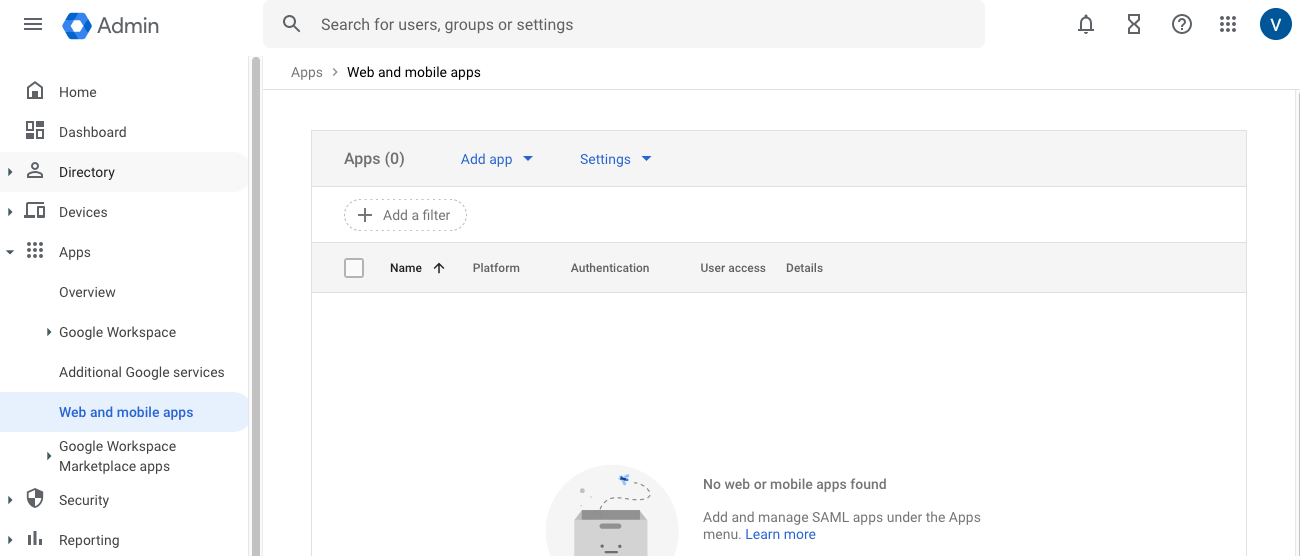
Click Add app then Add custom SAML app.
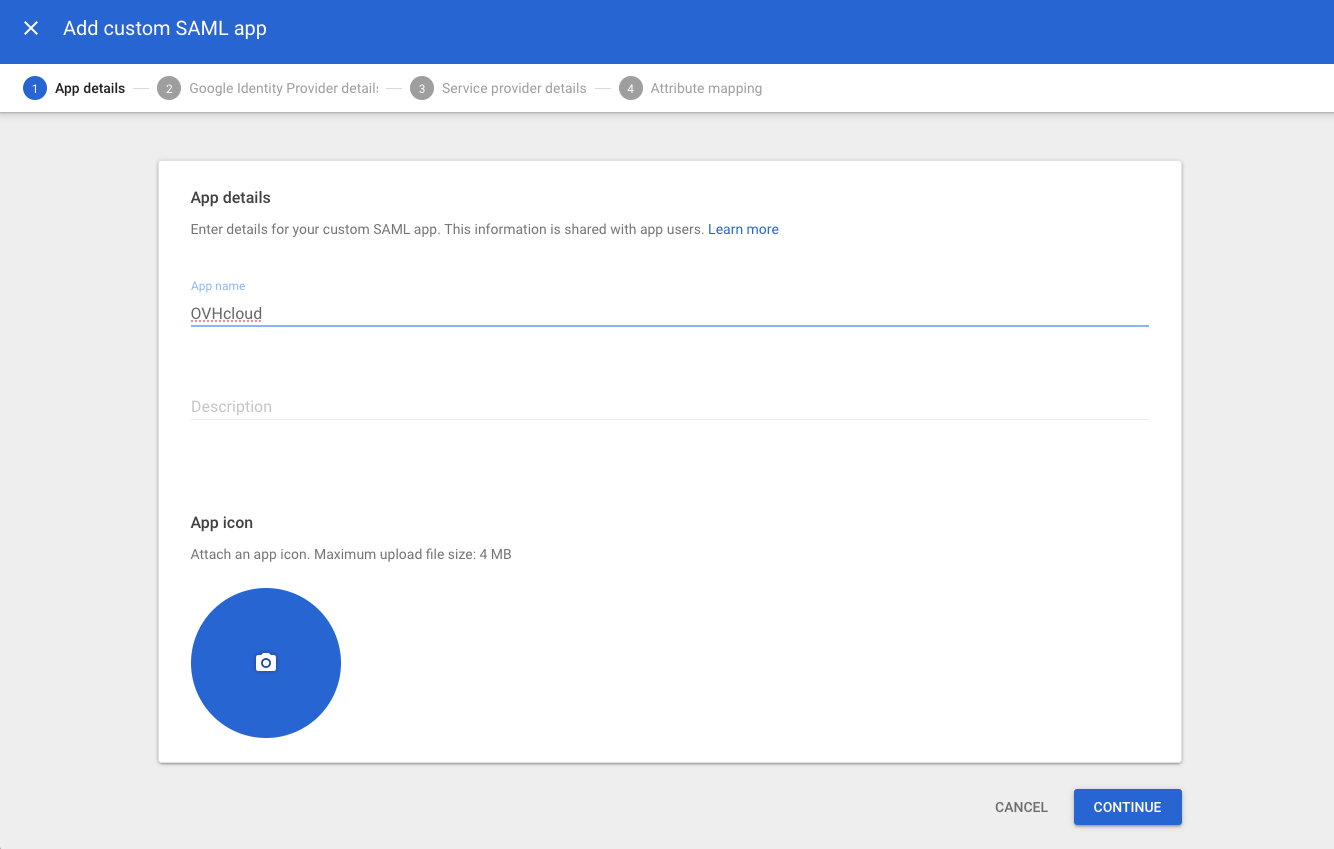
In the "App details" step, add a name for this interconnection, OVHcloud for example. Click Continue.
In the step "Google Identity Provider details", download the metadata file by clicking Download metadata then click Continue.

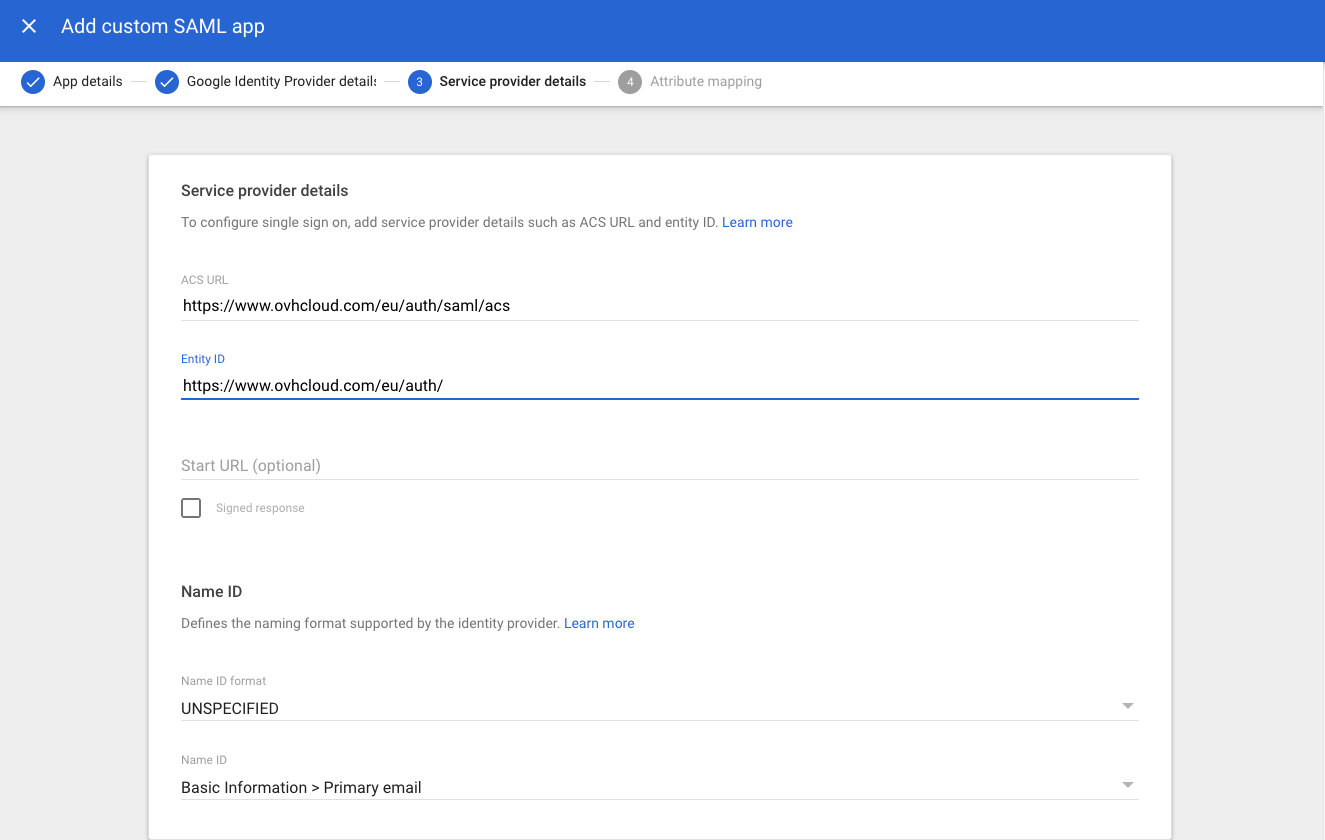
In the step "Service provider details", complete the ACS URL and Entity ID fields with the values for your region:
- EU region: ACS URL:
https://www.ovhcloud.com/eu/auth/saml/acsand Entity ID:https://www.ovhcloud.com/eu/auth/ - CA region: ACS URL:
https://www.ovhcloud.com/ca/auth/saml/acsand Entity ID:https://www.ovhcloud.com/ca/auth/
Click Continue.
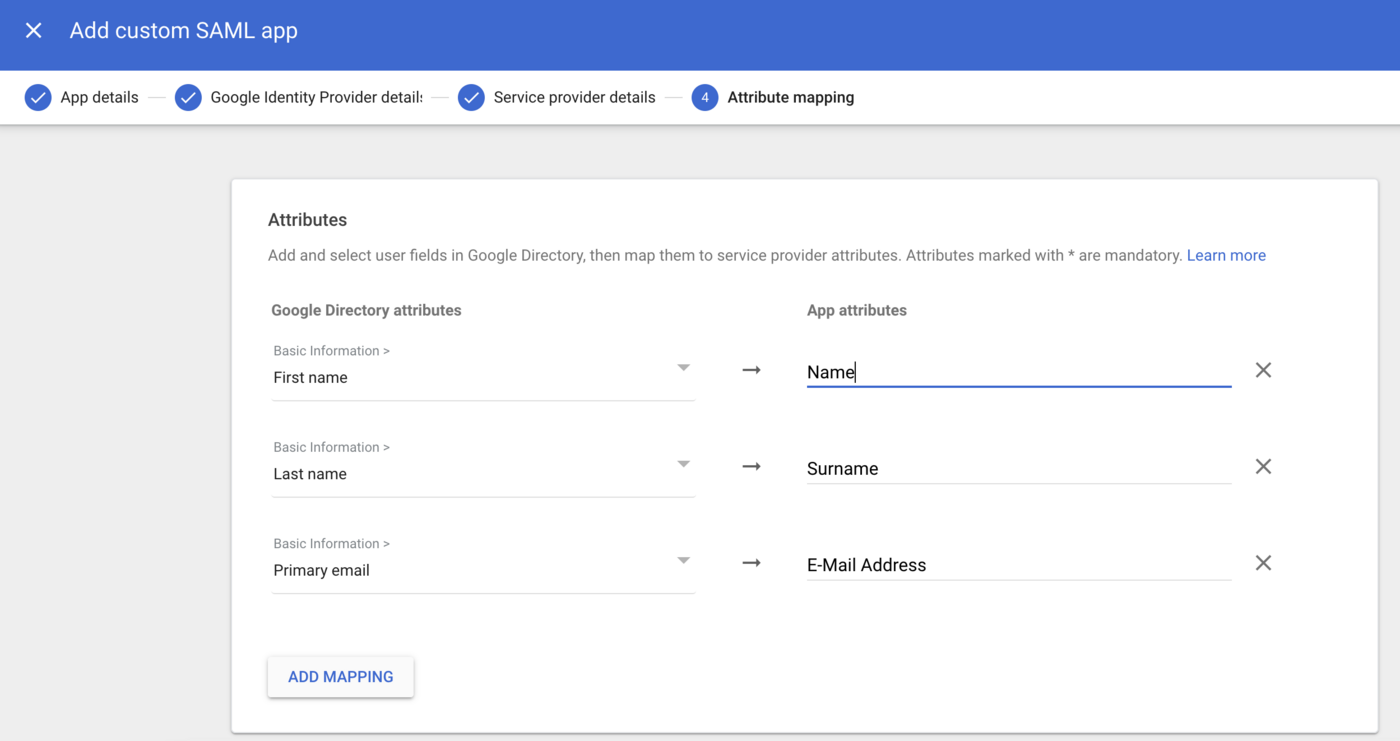
In the "Attribute mapping" step, add the following mapping:
- First Name: Name
- Last Name: Surname
- Primary email: E-mail Address
Click Finish.
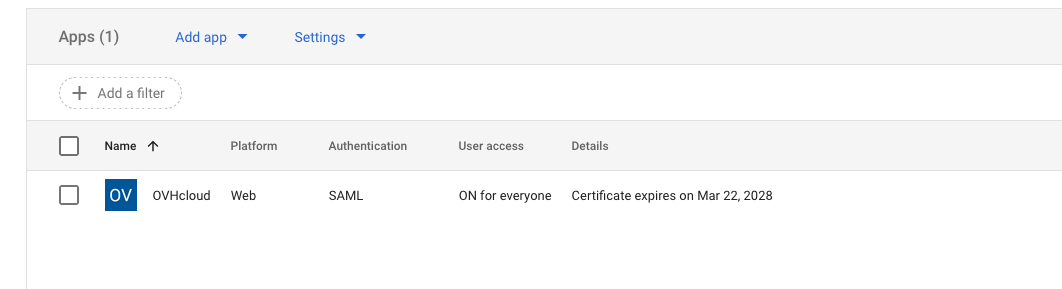
Enable access to this application by clicking OFF for everyone in the "User access" section. Click ON for everyone then the SAVE button.
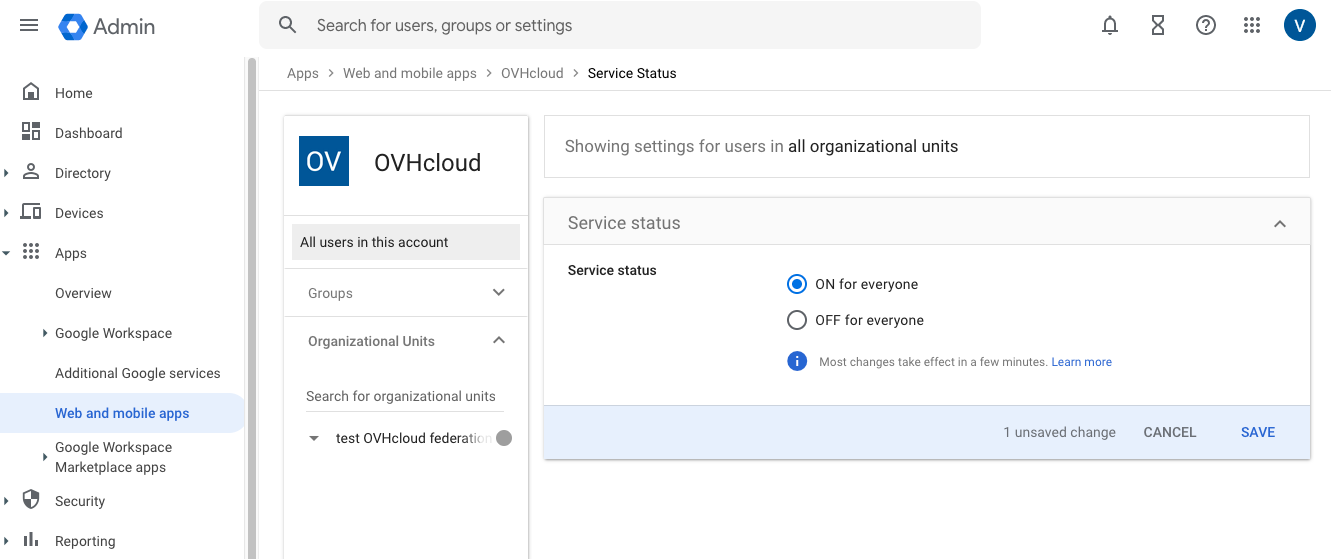
Adding application access to users can take several hours to take effect.
Your Google Workspace service now trusts OVHcloud as a service provider. The next step is to ensure that the OVHcloud account trusts your Google Workspace as an identity provider.
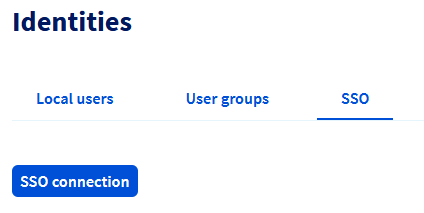
Registering Google Workspace into the OVHcloud account and configuring the connection
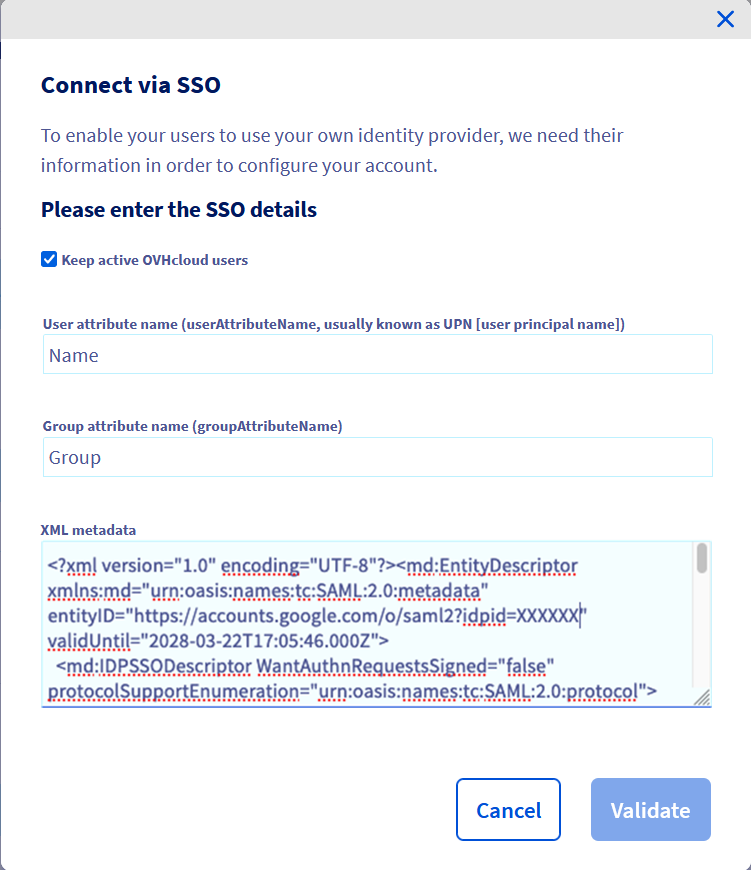
To add Google Workspace as a trusted identity provider, you need to provide the identity provider metadata in your OVHcloud Control Panel. Access the SAML SSO page, then click the SSO connection button.
Fill in the XML metadata of your Google Workspace service. Enter Name as the "User Attribute Name" and Group as the "Group Attribute Name". Click on Confirm.
You can keep local users by ticking the Keep active OVHcloud users box.
Now you need to retrieve your Google Workspace as identity provider, as well as default groups.
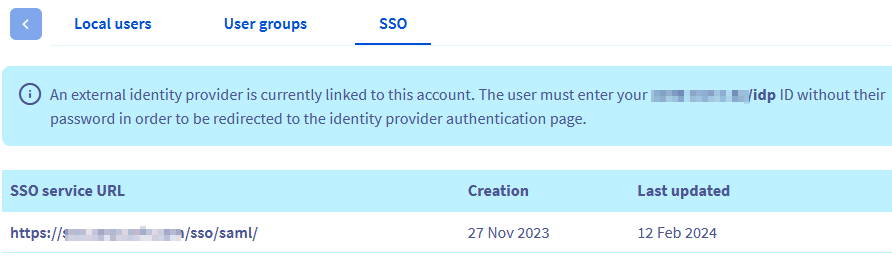
For more information, click on the link under “SSO Service URL”.
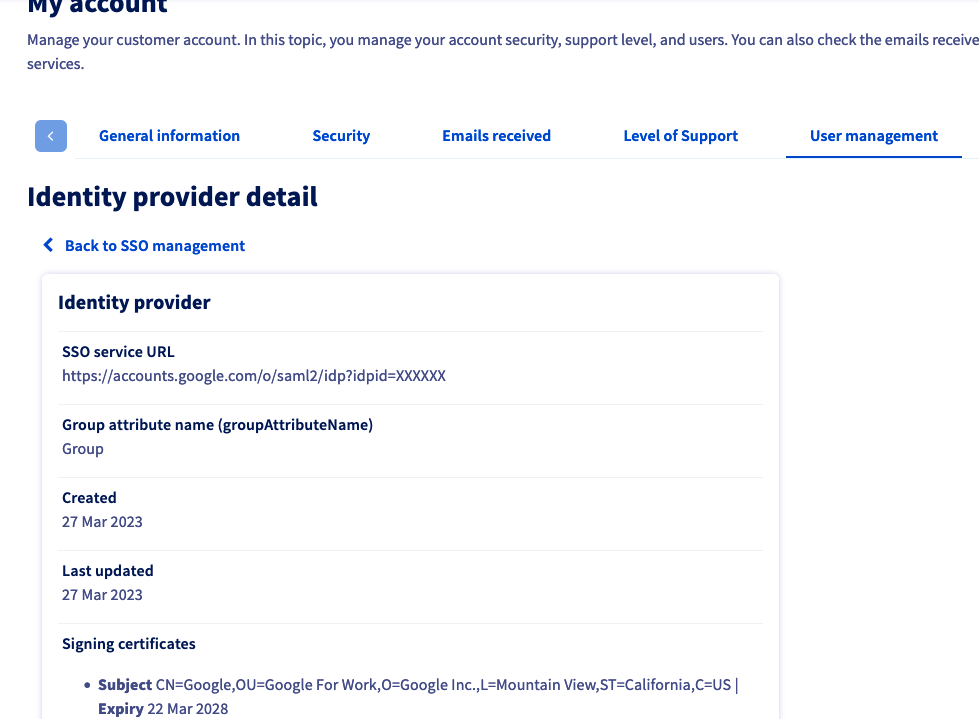
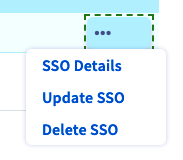
The ... button allows you to update or delete the SSO, and view its details.
Your Google Workspace is now considered a trusted identity provider. However, you still need to add groups to your OVHcloud account.
If you try to connect via SSO at this point, you will probably receive a Not in valid groups error message.
That is because your OVHcloud account checks whether the authenticating user belongs to an existing group on the account.
To resolve this, authorise the groups that will be transmitted from Google Workspace to OVHcloud. These groups are the same as those used to categorise your users.
To do this, log on to the Google Workspace administration interface with your administrator account.
Go to Apps then Web and mobile apps.
Click on the line for the application you added in the previous step.
Click SAML attribute mapping to edit the mapping of information shared between Google Workspace and OVHcloud.
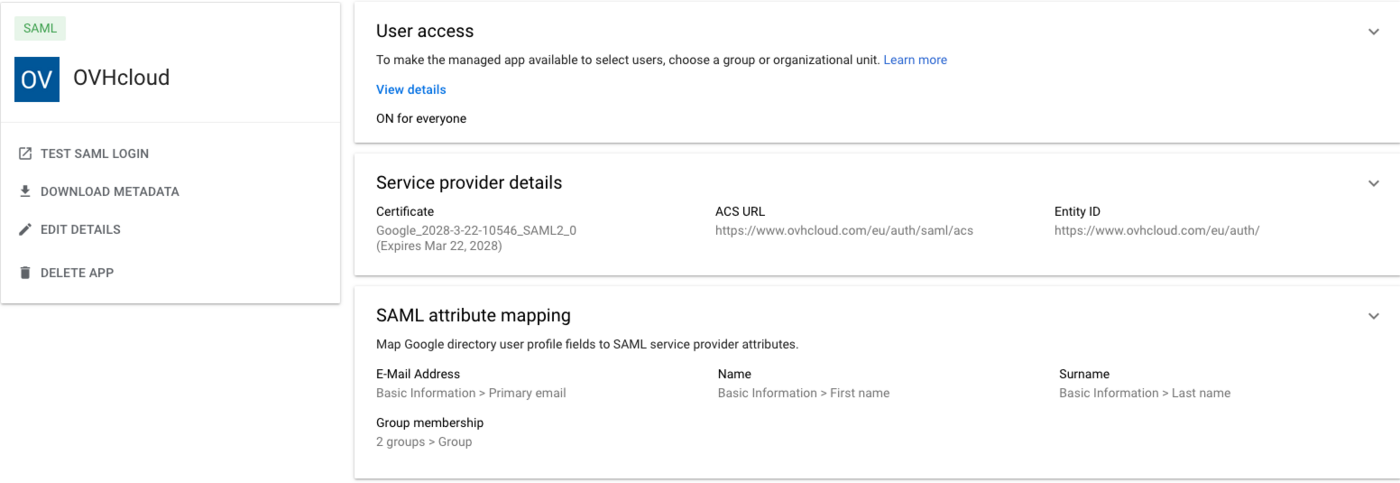
In the "Group membership (optional)" section, add any groups that you want to allow to connect to OVHcloud. In the "App attribute" field, enter Group.
You must then assign roles to these user groups at OVHcloud. Otherwise, your OVHcloud account does not know what the user is allowed to do and, by default, no rights are assigned.
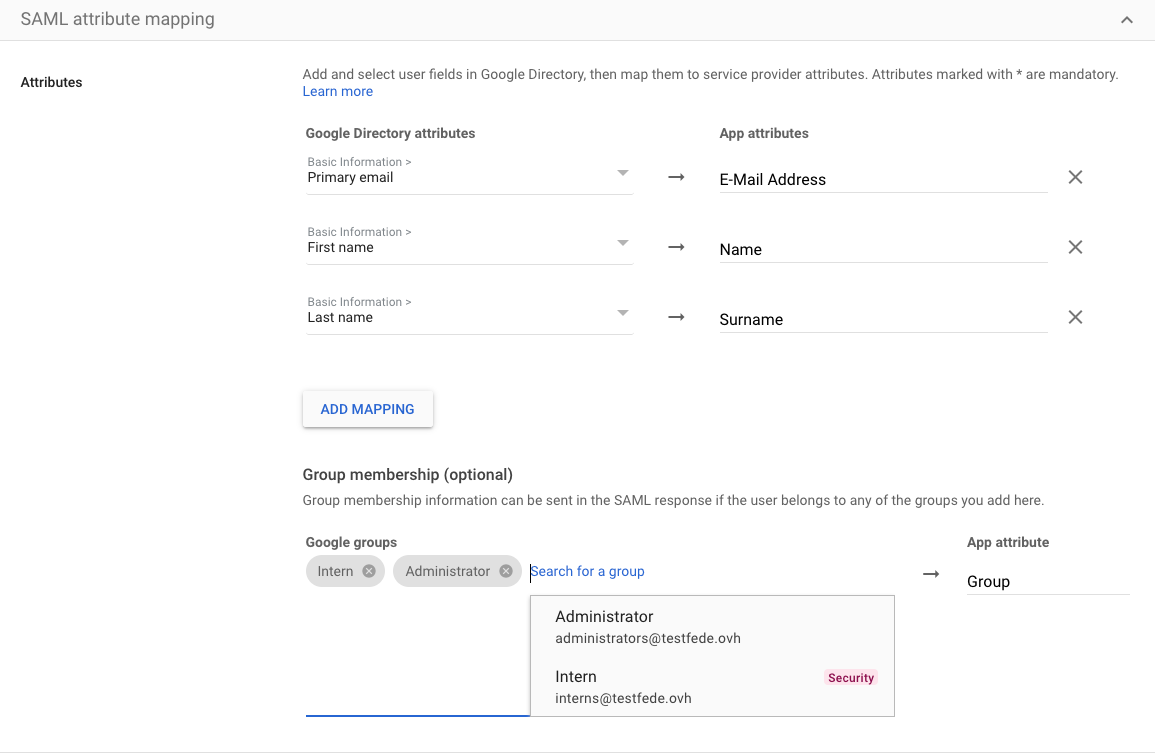
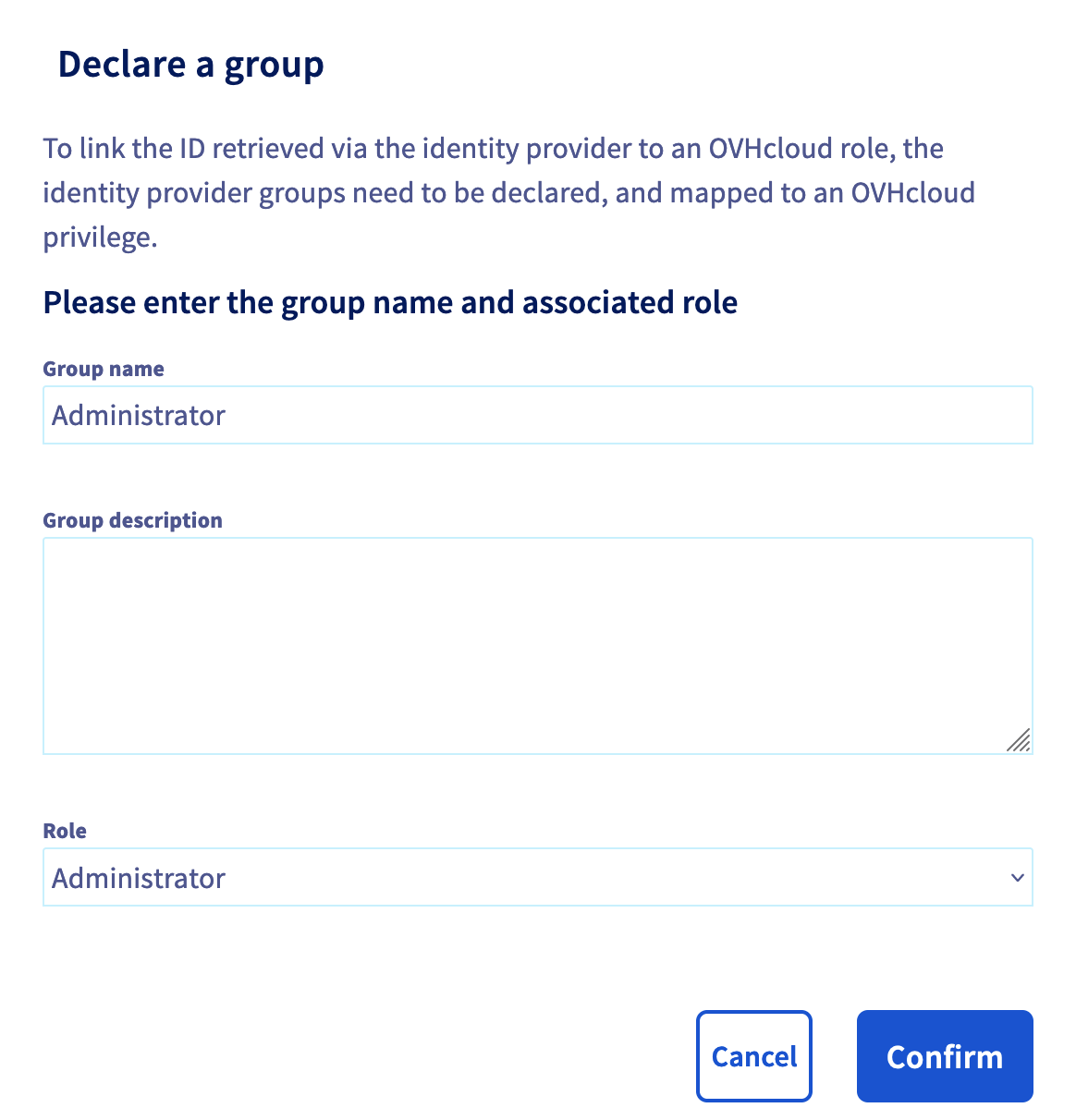
In your OVHcloud Control Panel, go to the Identities section, then the User groups tab. Then click the Declare a group button and fill in the fields:
- Group name: Group name within Google Workspace
- Role: Level of rights granted to this group
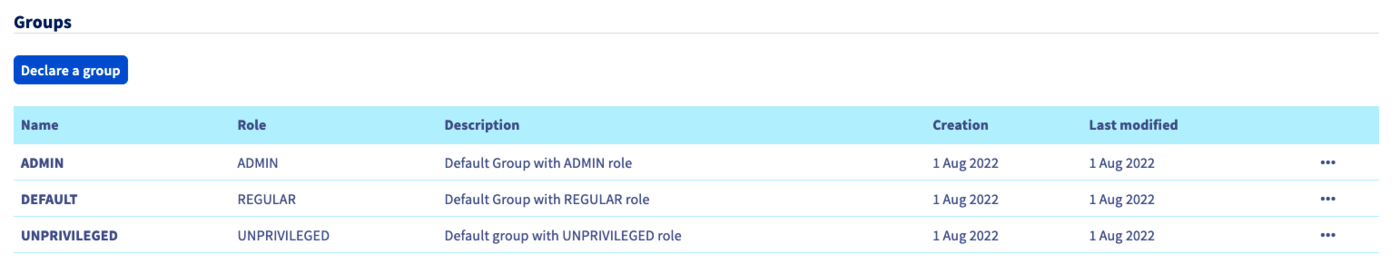
You can then verify that the group is added to your OVHcloud account in the "Groups" section:
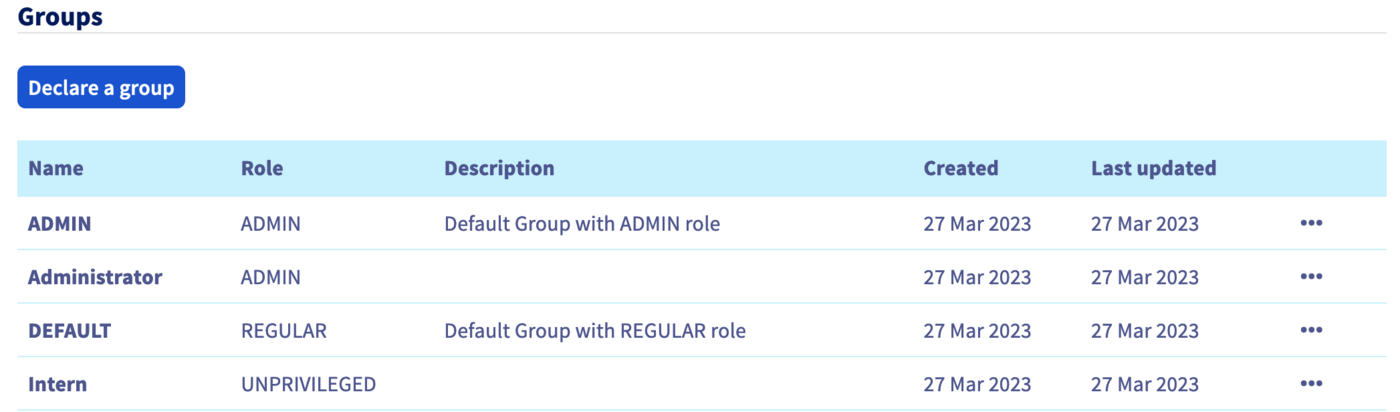
When you later log in with a user from the Intern group, your OVHcloud account will recognise that the user has the role "UNPRIVILEGED" specified by his group.
Warning: if you give the NONE role, you will need to assign permissions to this group via the IAM policies.
You will then be able to log out of your account and log back in with your Google Workspace as an identity provider.
Connecting via SSO
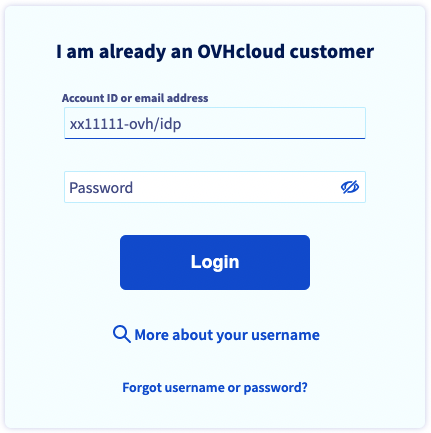
On the OVHcloud login page, enter your login followed by /idp without a password and click the Login button.
You are then redirected to your Google Workspace login page. Enter the login and password for a user of your Google Workspace, then click the Sign in button.
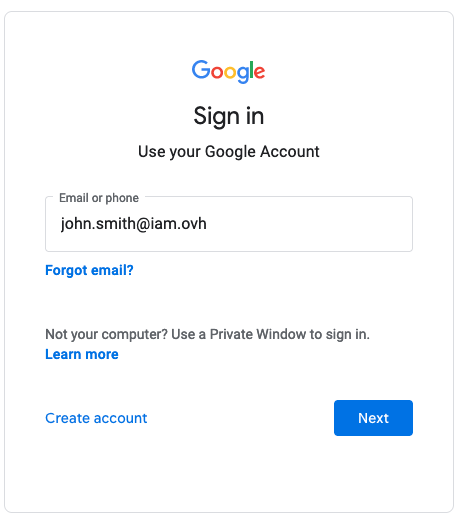
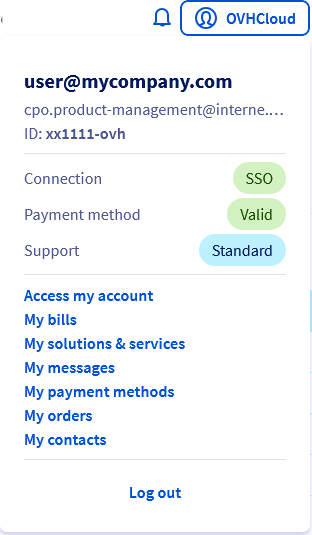
You are now logged in with the same customer ID, but through your Google Workspace user.
Go further
Securing my OVHcloud account and managing my personal information
Setting and managing your account password
Securing your OVHcloud account with two-factor authentication
How to use IAM policies using the OVHcloud Control Panel.
Join our community of users.